Ghosted Devices in 2026: The Hidden Endpoint Risk (& How to Eliminate It)
February 21st, 2024
3 min read
By Barry Angell

We talk a lot these days about Windows apps, but recently, I was reminded by an important customer of ours that, despite DaaS, VDI proliferation and the endless volumes of desktop software reporting back, we still have not solved the problem of lost or ghosted devices. Laptops, mobiles, cloud PCs, VDI, AVD session hosts, personal devices, IoT, contractor endpoints, and remote/hybrid fleets are just some of the devices we now need to track. But with so much complexity, one of the most dangerous and most overlooked risks is still the ghosted device.
Ghosted devices are endpoints that:
- Still appear in inventory but aren’t used
- Are unmanaged or out of compliance
- Have unknown patch status
- May have been lost, stolen, repurposed, or abandoned
- Still can access corporate apps, identity, or data
- Sit outside visibility, control, or lifecycle governance
In 2026, this risk is growing because organisations now have more device types, more remote endpoints, more identities, more update velocity, and a wider attack surface than at any point in the last decade.
This blog outlines why ghosted devices matter more in 2026, what’s driving the increase, and how modern EUC lifecycle orchestration tools (like Juriba DPC) can eliminate the problem completely.
Why Ghosted Devices Are a Critical Risk in 2026
1. Hybrid and Remote Work Has Increased Endpoint Sprawl
Hybrid work is now the norm, with 40% of UK employees working remotely (StandOut-CV, 2025). Hybrid job postings have grown from 15% in 2023 to 24% in Q2 2025 (Robert Half, 2025). Employees constantly switch locations, networks, and devices, increasing the risk of endpoints falling out of lifecycle governance.
2. Organizations Admit Endpoint Visibility Challenges
Recent research shows 75% of organizations struggle to manage remote endpoints, visibility, compliance, and risk (Cyber Magazine, 2024). Many cannot reliably track which devices are active, compliant, or even still present (Experteq, 2024).
3. Unmanaged Devices Are a Leading Cause of Breaches
Unmanaged endpoints are among the top causes of breaches, ransomware, and data exposure (SentinelOne). Nearly half of UK businesses have experienced security incidents linked to unmanaged devices (SecurityBrief UK). These ghosted devices are often unpatched, unenrolled, unmonitored, and still trusted by identity systems.
4. SaaS & Evergreen Update Velocity Makes Ghosted Devices More Dangerous
In 2026, SaaS apps update daily, Windows and browsers update monthly, and security threats appear weekly. A device that disappears for just 60–90 days can become heavily out-of-date, unpatched, and risky if it reconnects unexpectedly.
Why Ghosted Devices Still Happen (Even in Modern Environments)
Ghosted devices persist because:
-
Remote users stop using devices without returning them
-
Contractors churn quickly
-
VDI/AVD images fall out of sync
-
Cloud PC assignments drift
-
Laptops get replaced but never deprovisioned
-
Intune / UEM enrollment breaks silently
-
Stale objects remain in identity directories
-
Onboarding and off-boarding is inconsistent
-
Device-as-a-service vendors aren’t integrated into IT lifecycle workflows
Even organizations with strong endpoint security struggle because visibility does not equal lifecycle governance.
The Business Risks of Ghosted Devices in 2026
-
Compliance Failure: Ghosted devices undermine SOX, GDPR, DORA, cyber insurance posture, ISO 27001, and audit expectations.
-
Identity & Zero-Trust Weakness: Stale devices often retain cached credentials, old tokens, and outdated configurations, directly undermining zero-trust strategies.
-
Patch and Vulnerability Gaps: Unpatched, unseen devices rejoining networks can introduce critical vulnerabilities.
-
Data Leakage & Legal Exposure: Lost, stolen, or reused devices with sensitive data create data leakage and legal risks.
-
Technical Debt & Cost Waste: Ghosted devices inflate license/MDM costs, skew asset reports, and lead to unnecessary hardware spend.
The Modern Blueprint to Eliminate Ghosted Devices
Solving the ghosted device problem requires:
1. Real-Time, Cross-Platform Device Visibility
Track all endpoints—physical, virtual, cloud PCs, mobile, contractor/BYOD—across your environment. It’s not just about knowing who has a device, but whether it’s active, compliant, and secure.
2. Automated Lifecycle Governance
Implement automated offboarding, deprovisioning, compliance checks, reclamation, and workflow-driven device retirement. Dormant devices should be flagged, and stale objects removed from identity systems.
3. EUC Orchestration: Connecting Visibility to Action
Visibility and intelligence must be actionable. If a device is inactive, unenrolled, or out of policy, trigger automated workflows for remediation or retirement. Most enterprises lack this cross-system automation layer.
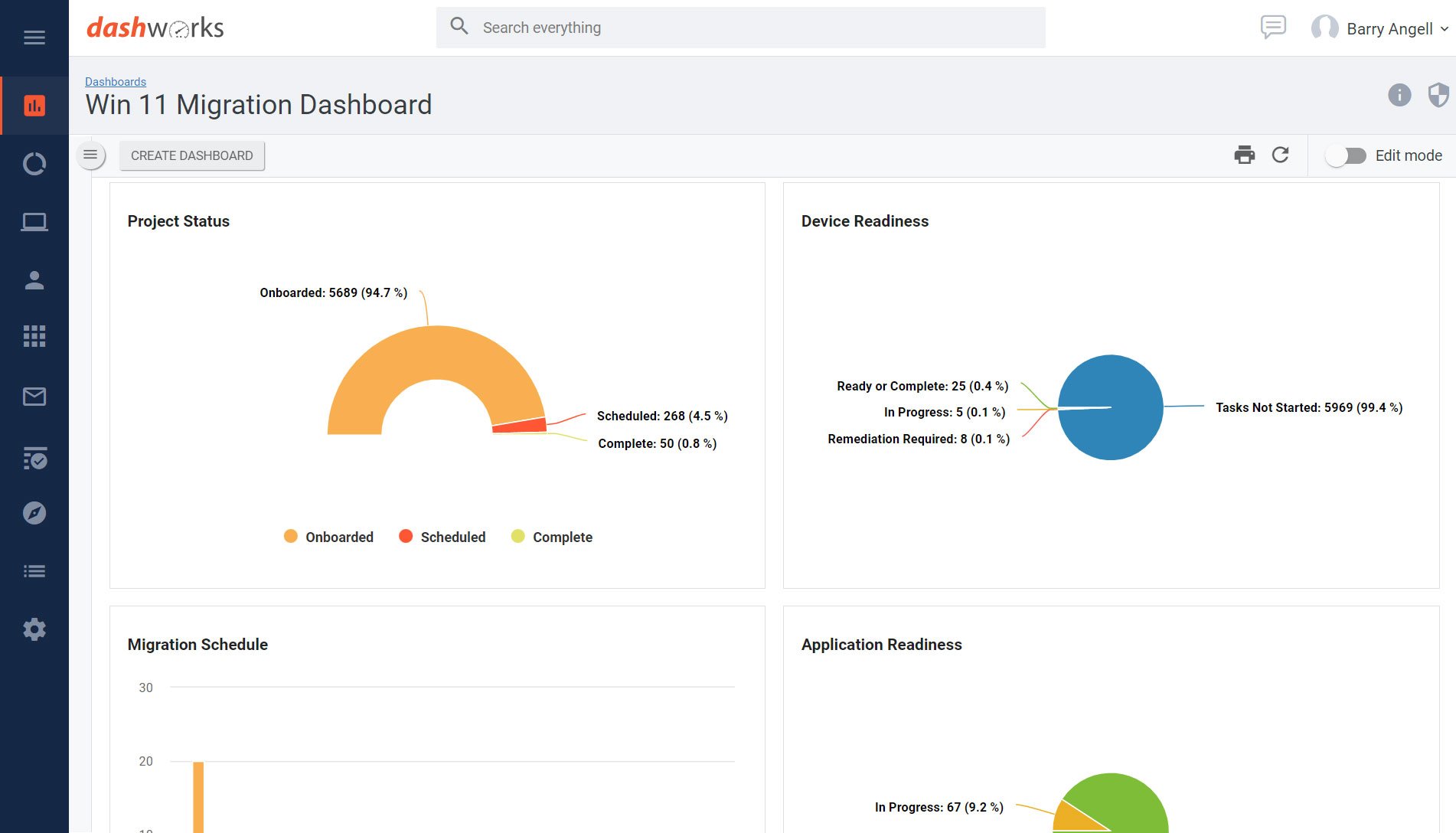
🧩 Where Juriba DPC Fits: Eliminating Ghosted Devices for Good
Juriba’s Digital Platform Conductor (DPC) provides:
-
Unified visibility across devices, apps, identities, and platforms
-
Readiness intelligence for active vs inactive devices
-
Automated workflows for deprovisioning, reclamation, and cleanup
-
Lifecycle orchestration across all endpoint types
-
Policy-based governance and continuous EUC hygiene
-
Persona-based targeting and stale asset monitoring
DPC transforms ghosted device cleanup from a manual audit into a continuous, automated discipline.
Internal Links & Further Reading:
Learn more about Juriba DPC and unified endpoint lifecycle management.
See also: 16 Questions You Need to Ask to Assess the Risk of Ghosted Devices
Conclusion
Ghosted devices are a symptom of missing lifecycle governance. With unified orchestration from Juriba DPC, organizations can eliminate ghosted devices, strengthen security, and ensure compliance.
Ready to eliminate ghosted devices? Request a demo or contact our team today.
Barry is a co-founder of Juriba, where he works as CEO to drive the company strategy. He is an experienced End User Services executive that has helped manage thousands of users, computers, applications and mailboxes to their next IT platform. He has saved millions of dollars for internal departments and customers alike through product, project, process and service delivery efficiency.




![What is a Digital Workplace? [Definition]](https://blog.juriba.com/hs-fs/hubfs/What%20is%20a%20Digital%20Workplace%20%5BDefinition%5D.jpg?width=1600&height=900&name=What%20is%20a%20Digital%20Workplace%20%5BDefinition%5D.jpg)