Below is a summary of some popular compliance standards and regulations enterprises must frequently consider in the adoption of new and updated software.
- Financial Regulations (e.g., Sarbanes-Oxley Act, Basel III):
- Example: A new version of a financial reporting tool may not adhere to the stringent data accuracy and audit trail requirements mandated by Sarbanes-Oxley.
- Implication: This could lead to inaccurate financial reporting, legal repercussions, and a loss of investor confidence.
- Accessibility Standards (e.g., ADA, WCAG):
- Example: An update to the organization's website or client-facing applications that fails to comply with WCAG 2.1 AA standards could make the application inaccessible to individuals with disabilities.
- Implication: This could lead to legal challenges under the ADA and damage the organization’s inclusive reputation.
- Industry-Specific Standards (e.g., ISO 27001, PCI DSS for Payment Systems):
- Example: An update to a payment processing system might not be compliant with PCI DSS standards, potentially leading to vulnerabilities in handling credit card information.
- Implication: Breaches could result in hefty fines, legal action, and loss of customer trust.
- Export Control Regulations (e.g., ITAR, EAR):
- Example: A software update could inadvertently allow users in embargoed countries to access controlled technology or data, violating ITAR or EAR regulations.
- Implication: This could lead to severe legal consequences, including fines and sanctions.
- Data Protection and Privacy Laws (e.g., GDPR, HIPAA):
- Example: An update to a healthcare management application might introduce features that inadvertently share patient data with third-party vendors, violating HIPAA regulations.
- Implication: Non-compliance could result in significant fines and damage to the organization's reputation.
- Industry Compliance (e.g., FERPA in Education):
- Example: A new feature in an educational app might inadvertently expose student records, breaching FERPA guidelines.
- Implication: Non-compliance could lead to federal funding cuts and legal issues.
In conclusion, the role of an Application Owner is multifaceted, encompassing technical management, compliance adherence, and strategic decision-making. Understanding security updates, compliance standards, and the implications of software changes are crucial for ensuring a smooth and secure operational environment.
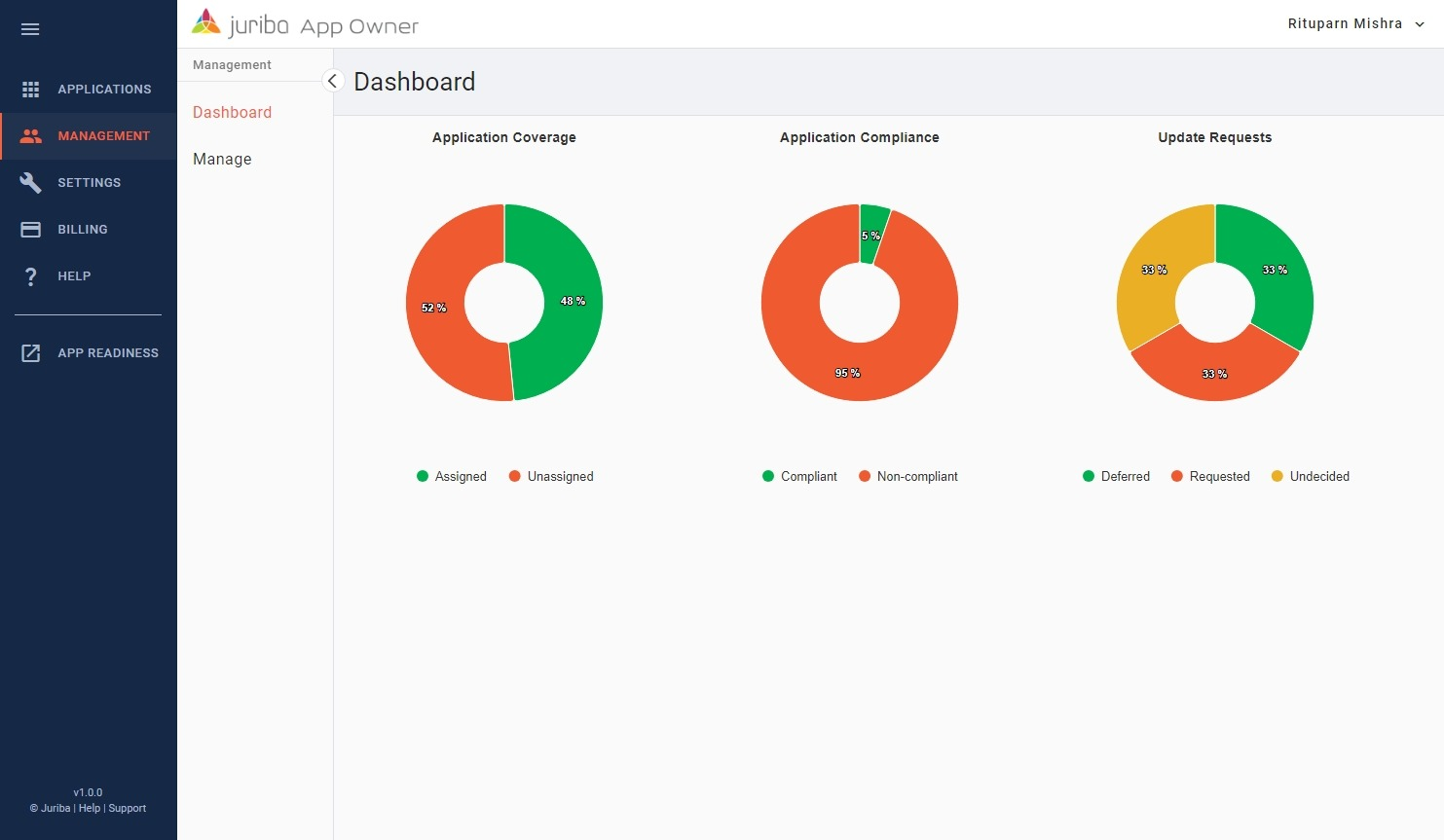
By staying informed and proactive, Application Owners can navigate the complexities of software management effectively. If you're eager to delve deeper into this vital role and stay ahead of the curve, we've just released Juriba App Owner so don't miss out on the opportunity to enhance your expertise and significantly impact the field of application ownership.
Topics: